The next step to building an API is to protect it from anonymous users. Azure Active Directory (AD) serves as an identity platform that can be used to secure our APIs from anonymous users. After the authentication is enabled, users will need to provide a OAuth 2.0/ JST token to gain access to our API.
Let us begin to implement Azure AD Authentication in ASP.NET Core 5.0 Web API.
I will be creating ASP.NET Core 5.0 project and show you step by step how to enable authentication on it using Azure AD Authentication. We will be doing it using the MSAL package from nuget.
Prerequisites
Before you start to follow steps given in this article, you will need an Azure Account, and Visual Studio 2019 with .NET 5.0 development environment step.
Creating ASP.NET Core 5.0 web application
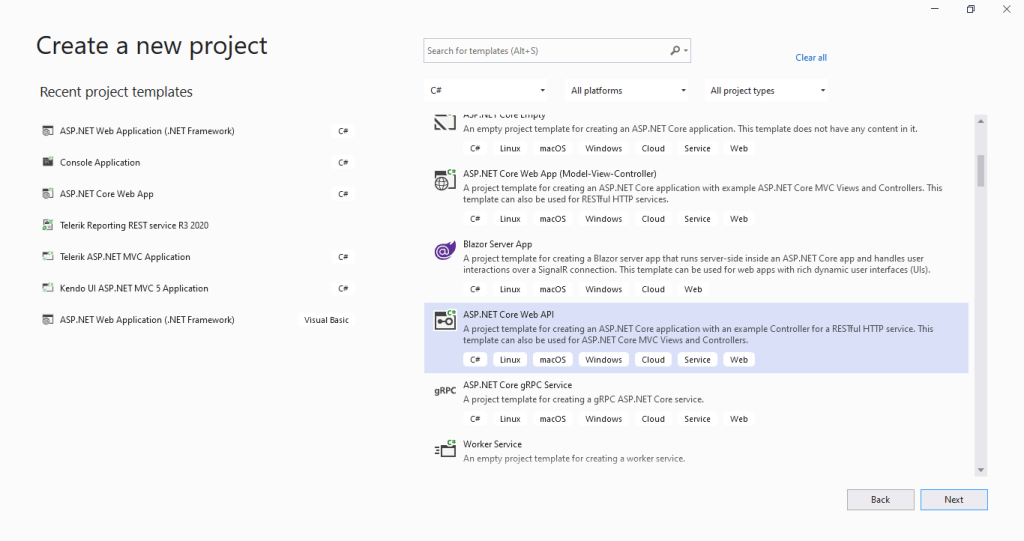
Open visual studio and click on Create a new project in the right and select “Asp.net core web app” as shown in below image and click next.
In the configure your new project section enter name and location of your project as shown in below image and click next

In the additional information step, select .NET 5.0 in the target framework, Authentication Type to none and check Configure HTTPS checkbox and click on create.

Configuring ASP.NET Core 5.0 App for Azure AD Authentication
Open appsettings.json of your web api and add following lines of code.
"AzureAd": {
"Instance": "https://login.microsoftonline.com/",
"Domain": "gtmcatalyst.com", "qualified.domain.name",
"ClientId": "your-client-id",
"TenantId": "your-tenant-id"
}Replace your-client-id and your-tenant-id with the actual values that you copied while doing app registration in azure ad
Next, add package manager console and add following two package references to your web application.
using Microsoft.AspNetCore.Authentication.JwtBearer;
using Microsoft.Identity.Web;Next, open startup.cs in your project and paste following code in the ConfigureServices method
services.AddAuthentication(JwtBearerDefaults.AuthenticationScheme)
.AddMicrosoftIdentityWebApi(Configuration.GetSection("AzureAd"));Next, in the Startup.cs, go to Configure method and add app.UseAuthentication(); line before app.UseAuthorization(); line.
Next, open any Controller and add [Authorize] attribute:
[Authorize]
[Route("[controller]")]
[ApiController]
public class SupportController : ControllerBase
{
}Save all files and run your project.
You will notice that once you run the project, and try to access any method in support controller from the browser you will get return the HTTP ERROR 401 ( Unauthorized client error).
Conclusion
Our API is no longer available for anonymous access. It is now protected by Azure AD Authentication.

